What is Role-based Dashboard Access Control?
Role-based dashboard access or admin panel empowers the super admin to assign roles to colleagues and teammates allowing them to have limited access to dashboard features. This eliminates the risk of exposing sensitive admin information while complying with the least privileged principle. Role-based access control ensures that employees and team members can complete their jobs without putting production applications or sensitive information at risk.
Role-based dashboard access or admin panel offers features like login authentication, email verification, user roles and permissions, forget/reset/change password, admin profile management, and more to control data and information access for enhanced security.
The Primary objective of creating dashboards or admin panels with role-based access is to securely give your end users an interface to access the information over a single unified frontend tool where they see only the details they need to perform their tasks while your source data remains unaltered and intact.
For instance, say you run an eCommerce website over Shopify, use Stripe as your payment gateway, PostgreSQL as your database, and Google Forms as a means for customers to write to you in case they need support. Now say your customer support team receives a query to return and refund via one of the Google forms; they need to access all the other tools to pull up orders, payments, and delivery partner details! This potentially leads to delays in resolution, dependencies on database administrations, and the business team in charge of the individual tooling.
With a custom admin panel that can create role-based views for your customer support team; you can easily give them access to all the critical data points they need to solve this challenge at speed.
> Here’s a ready template https://www.dronahq.com/templates/Customer-Support-Tool-/
Why Use Role-Based Views?
Not all users of your organization will have the same exact needs. For example, both your marketing manager and sales head might need access to your CRM platform, but how they use the platform may be different. Giving both of them access to all parts of the system may bring unnecessary security risks while making it more difficult for the users to carry out their designated tasks. Role-based access ensures that each user has the exact permission they need to complete their job. This can help organizations balance security, efficiency, and ease of access.
Providing users with access to data through views rather than providing them with direct access to database tables is important for two primary reasons :
Views provide simple and granular security
Admins can use a view to limit the data that a user is allowed to view in a table. For example, if you wish to provide specific users with access to records of full-time employees in an employee’s table, you can create a view containing only those records. It is simpler and easier than creating and maintaining a shadow table while ensuring data integrity.
Views simplify the user experience
Administrators can hide viewing complex details of database tables from end-users who do not need to see them. Users will not see the table columns that aren’t selected by the view if the user dumps the contents of a view. This saves them from the confusion caused by cluttered designs, poorly named columns, table keys, and unique identifiers.
History of Role-Based Access Control
Moderating access to roles and responsibilities in commercial computer systems has been in use since the 1970s. However, these procedures were ad-hoc and had to be redesigned for each new system on a per-case basis.
The system of role-based access control was formalized in the year 1992 by researchers at the American National Standards Institute (NIST). Ferraiolo and Kuhn laid the foundation in a paper outlining a general-purpose access control methodology for both civilian and commercial use.
Ferraiolo, Kuhn along with other researchers continued to refine RBAC throughout the 1990s and early 2000s. They built on earlier work to explore the economic benefits of RBAC, outlined a unified model, and defined separation of duty forms. NIST officially adopted RBAC as an industry-standard in 2004.
Key Components of Role-Based Access Dashboard And Admin Panels
Role-based dashboard access or admin panel control is based on some key components that determine the interactions between users and the data or resources they are trying to access. These components may vary across organizations,
Users
Users are the entity asking for access. They may or may not actively ask for access. A request may be initiated automatically when a user logs into the system.
Roles
Roles are an aggregate function of multiple user traits in RBAC, which are based on their job designation. Roles determine what privileges and permissions are assigned to a user. They generally exist in hierarchies. A superior role gets more privileges than a lower role in the hierarchy. For example, a document owner has full control and privileges over their document. They can edit, share, save, etc, while a contributor may only get the right to view the document. Here, the owner’s role is superior to the contributor’s role.
Operations
Users can request access for mainly two things- operations and objects. Operations mean any activity or process in a computing environment. For example, changing the discount codes applied to certain inventory items; this operation needs to be executed by only certain pre-approved end users. In DronaHQ you can configure what elements of the user interface the end user sees (read more here). So say you configure a workflow upon click of a button to update discount codes to inventory items, you can choose to show that button only to the end user marked as your primary admin.
Permissions
Permissions are a set of business rules specifying which apps, operations, APIs, and data a role can access. For example, if an employee is assigned the creator role, permissions refer to the list of actions that the user is allowed to perform in that role. As a creator, they may be able to only edit the apps but are not allowed to publish, share, or delete them.
The RBAC Model types
Core RBAC
The core model can stand alone as an access control method while laying the foundation for both the hierarchical and constrained models. All RBAC must follow these 3 rules:
Role Assignment: A subject can exercise permission only if they have been selected or been assigned a role.
Role authorization: All subject’s active roles must be authorized.
Permission authorization: A subject is only allowed to exercise permission which is authorized for the subject’s active role.
Hierarchical RBAC
As the name implies, hierarchical RBAC implements a hierarchy within the role structure establishing the relationship between roles. Users with senior roles acquire permissions for junior roles which are generally assigned to their subordinates. The needs of the company determine the complexity of the hierarchy.
Constrained RBAC
Constraint RBAC adds separation of duties (SOD) to a security system. SOD is a popular security practice where a single duty is spread among several employees. Under SOD, a single user cannot hold mutually exclusive roles as defined by the organization. This helps in enforcing the two-person rule where two distinct users are required to authorize an action.
Example of Role-based Dashboard Access and Admin Panel control
RBAC lets you control what end users can do both at the broad and granular levels. Admins can designate and assign roles and align them with access permissions as per the employee’s position in the organization. If an end user’s job role changes, you may need to manually assign their role to another user.
These can be some of the designations in an RBAC tool:
- Management role group: can add or remove members.
- Management role scope: limits the apps and APIs the role group is allowed to manage.
- Management role tasks: Actions that can be performed only by a specific role group.
- Management role assignment: links a role to a role group.
If a user is added to a role group, they have access to all the roles in that group. This access becomes restricted when the user is removed from the group. Users can also be assigned to multiple groups. They may get temporary access for specific projects and get removed once that is complete.
Other options for user access can be:
- Technical: assign to users in the technical group
- Primary: primary contact point for a specific account or role.
- Billing: access to the billing account.
- Administrative: access to users performing administrative tasks.
Managing Role-Based Access Control
The RBAC will change at various stages of the user’s journey in the organization. New users will join, get promoted, or leave the organization, this means their RBAC status will also change according to their position.
As your organization grows in complexity, you will need to modify your roles as well. This is where iterative adjustment and regular review will play a crucial role. It is important to collect feedback and monitor your security status on a regular basis. Conduct periodic reviews of roles, role assignments and RBAC authorization. Look out for-
- Roles with unnecessary access to a sensitive resource.
- Users attempting to access data outside their scope.
- Overlapping role assignments.
- Role explosion.
RBAC Implementation
For the effective implementation of RBAC, you can treat them as defined in the following steps.
- Understand your business needs—before moving to RBAC, you should examine job functions, supporting business processes and technologies by doing a comprehensive needs assessment
- Plan the scope of implementation— identify the scope of your RBAC requirements and plan the implementation accordingly to align with the organization’s needs. Focus on systems on applications that store sensitive data.
- Define roles—Watch out for common role design pitfalls like excessive or insufficient granularity, overlapping role assignments, role explosions, and granting too many exceptions for RBAC permissions.
- Implementation— You can do this in stages to reduce workload and disruption to the business. Before focusing on increasing granularity, start with coarse-grained access control.
Implementing role-based access in DronaHQ
In DronaHQ role-based access control works on two levels:
- App end-user level – Setting up permissions for end users based on their user credentials as well as their roles. This can be controlled to very minute details – for example, developers can control which UI component the end user sees based on their role.
- Admin level – Setting up admin permissions based on who can access, edit, save changes, and publish the apps and APIs
Say you need admins to see some parts of an app or be able to assign tasks to users who were part of a group. Traditionally you’d hand code this into the object but as your team grows and operations scale, this can go out of date quickly and cause mistakes.
Out of the box, DronaHQ allows you to configure user groups and assign your end users to groups to determine how individual users access an app or an API integration. To further that, the platform also supports conditional visibility rules that lets app makers control what UI aspects of the app the end user can interact with and what remains concealed (if a user is this then hide/show that).
App and Connector Permissions
To limit access to data you can create different teams like Customer Support which has access to Tickets, or Sales Team has access to customers, orders, etc. You can create multiple teams with different Roles (Administrator, Editor, or Read-only).
With DronaHQ you can assign specific permissions to people who can access, edit and own the applications and connectors. Users may be given authorization as Owner, Editor, Use only, or None by the Owner.
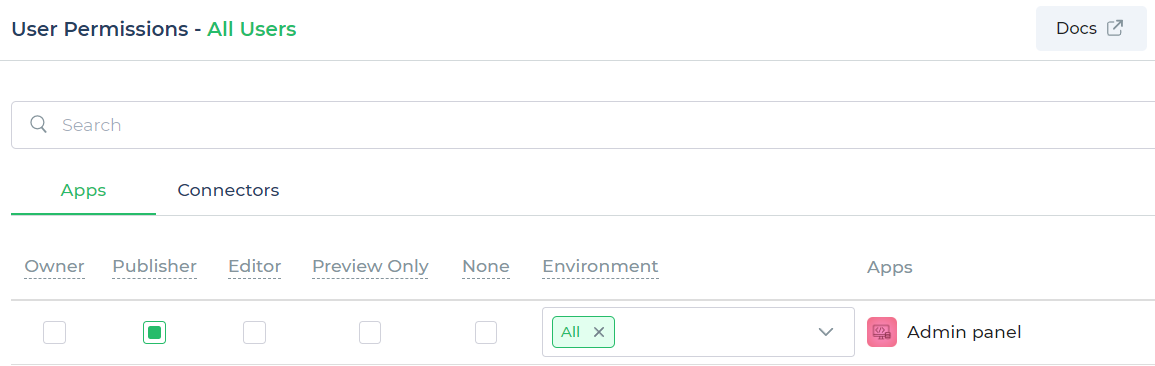
App Permissions
There are five types of App permissions in DronaHQ
1) Owner –
Owner role has the maximum permissions possible. This role allows a user to edit app details, update app, change status of app to live, Edit environments and delete app.
2) Publisher –
This role allows a user to edit app details, update app and change status of app to live. Publisher won’t be able to change user permissions and delete the app.
3) Editor –
This role will only allow users to edit app and to preview the app. Editor won’t be able to publish the app.
4) Preview Only –
This role will only have permission to preview the app. User won’t be able to edit or publish the app
5) None –
This role will not have any permissions and hence the app won’t be visible to people in the studio dashboard.
For more details on Apps and Permissions, please visit here.
Connector Permissions
The Owner can assign permission to users as Owner, Editor, Use only or None. It is important to know what the term owner stands for in different contexts
- Account owner: Has blanket access to all resources.
- App owner: The one who creates the app and can give permissions.
- Connector owner: The one who creates the connector and can give permissions.
There are four types of connector permission offered by DronaHQ-
- Owner- Owners have the maximum permissions. They can allow a user to edit permissions of their users, edit configurations, delete connectors and manage the environment.
- Editor- The editor can edit configurations of connectors and manage environments.
- Use Only – This user will only have permissions to use. If a user tries to edit the connector, the changes will not be saved.
- None- This user will not have any permissions at all. The connector will not be visible to people having this role.
Benefits of RBAC
Reducing administrative work and IT support
The need for paperwork and password changes when an employee is hired or changes their role can be reduced with RBAC. It can be used to switch and add roles quickly and implement them across operating systems, platforms and applications.
Optimizing operational efficiency
RBAC offers a streamlined approach to access control. All the roles can be aligned with the organisational structure so that users can do their jobs more efficiently and autonomously.
Improving statutory and regulatory compliance
With RBAC, companies can more easily meet statutory and regulatory requirements for privacy and confidentiality since IT departments and executives have the ability to manage how data is accessed and used.
Improved risk management
Data security and privacy are one of the top most concern of modern businesses. Data leaks and other security breaches can cause massive harm to any organisation. Role-based access control can help organizations reduce these risks by only allowing specific users to access sensitive data. This can also help in limiting the impact of damage when things go wrong.
Scalability
RBAC offers both vertical and horizontal levels of scalability, which means there are minimum barriers while adding or updating user roles. RBAC offers easy implementation of changes and modification of existing roles rather than asking for permissions on a user-by-user basis.
Disadvantages of Role-Based Access Control
Requires Business Knowledge
RBAC requires a clear understanding of the ideal structure of the organization as well as the technical infrastructure that supports it. This can be a challenging task in large or growing organizations when IT or security managers are expected to define roles without the help of HR or decision-makers.
Demands Careful Implementation
RBAC needs thoughtful and careful implementation. Administrators need to have 360 degrees of knowledge of the hierarchical structure and understanding of job roles for effective RBAC implementation. There can be numerous confusing scenarios when you have to decide which roles best suit a user.
Can lead to role explosion
Role explosion can arise when real-world roles and access needs differ from the ones outlined in the policy documents. Temporary roles can stick around longer, admins may forget or leave some roles, and job positions may change leading to chaos and confusion.
Role-based access control best practices
Develop an RBAC Strategy
Start by evaluating your systems, data or processes in your organization. Would they benefit from access control? Analyze job functions, technologies and business operations to identify the need for RBAC. Next, decide how you will use RBAC. What will be the outcome of this process? Finally, note any gaps you need to address. What are the regulatory requirements you need to meet?
Analyze Your Workforce
Evaluate all the roles in your organization. Design a set of roles that align with company goals by taking the entire workforce into consideration. Going for a top-down approach would help you to address the functional needs of each role.
Create and Define Roles
Now that you have done all the groundwork, it is time for implementation. Reconcile your lists and map the result of your workforce analysis to the resources from your inventory according to the principle of least privilege. This mapping will help you create and define your roles.
Establish a Governance Structure
You need to establish a decision-making body to maintain all the roles you have defined. Try to establish them in writing, and identify project priorities standards that serve the best interests of your organization.
DronaHQ’s powerful role-based dashboard access and admin panel control enable admins to manage user roles according to role hierarchy while providing utmost security. Sign up now for a free trial!