Mailchimp’s internal tool security breach teardown
A recent attack on mailchimp’s internal tool led to compromise of 300m+ email ids of their customer. As per their CISO
In addition to viewing accounts and exporting data, the threat actors gained access to API keys for an undisclosed number of customers, which have now been disabled and can no longer be used.
Such leaks can have serious financial as well as credibility ramifications. Internal tools are generally a soft target for a simple reason — they aren’t given the kind of attention that it deserves.
Let’s dig a bit deeper in the leak — an API key got compromised. So here are the some of the possible critical issues with the this internal tool:
- – Key was sniffed out of the frontend code
- – API call was made from the frontend application & the key was present in the call and the end user was using the tool from public internet (some coffee shop)
- – Key was loosely communicated & accidentally made its way to the attacker (very unlikely)
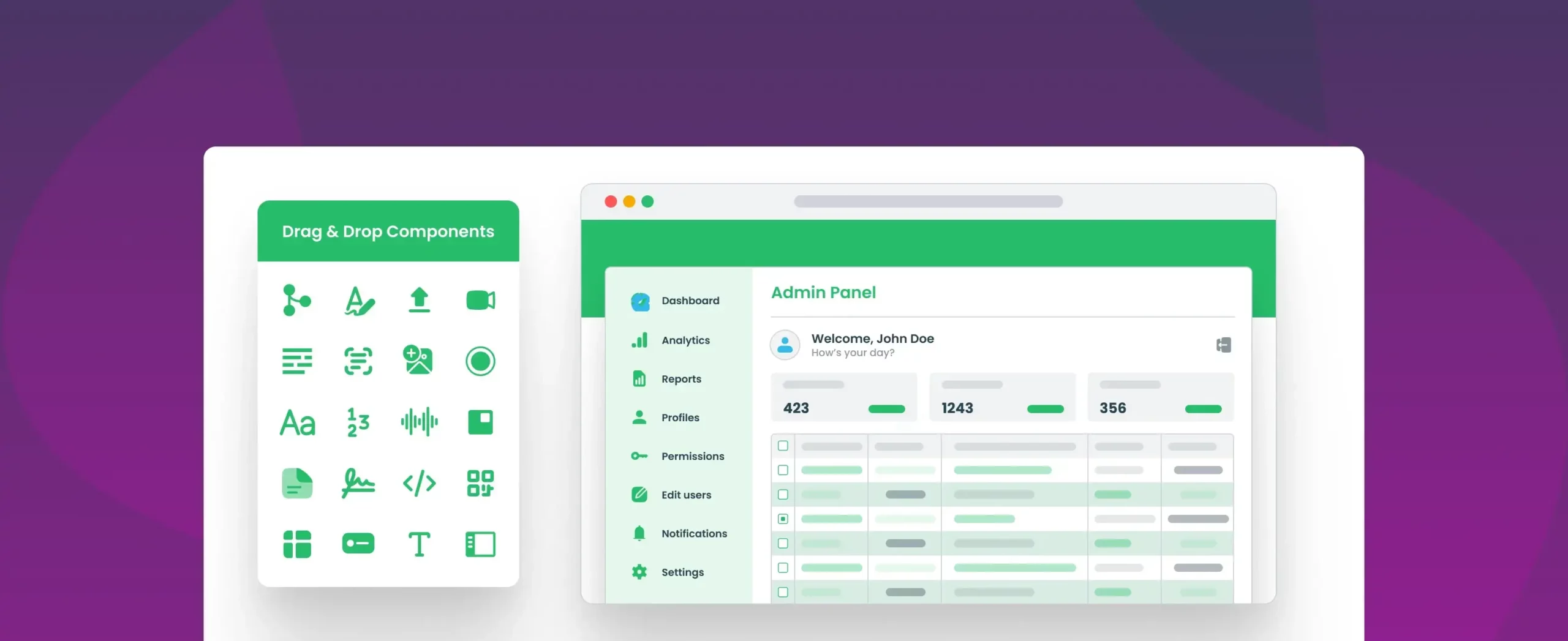
To thwart against any of the 1st two possibilities — internal tools must be backed by a middleware to route traffic so you can avoid such problems. Tools made using modern tools like DronaHQ ensures that all API calls are actually made through a secured middleware layer.
Also additionally mailchimp’s internal app lacked controls to time limit the exposure of the API key. These could be some of the possibilities of loose controls:
- – Key didn’t have a TOTP or oAuth mechanism for enhanced protection
- – Parameters in the api call weren’t encrypted
At DronaHQ we do carry out yearly security reviews of the tool and a sample of apps made by the tool. This helps us stay a step ahead and help our customers build secured internal tools. It would be a good practice to conduct such reviews periodically on all your internal tools to protect against such embarrassing events if you are building internal tools with traditional approach!